Europe is witnessing an alarming surge in “wrench attacks” – violent crimes where criminals physically coerce cryptocurrency holders into surrendering their digital assets. These brutal incidents, named after the hypothetical scenario of threatening someone with a wrench until they reveal their crypto wallet keys, represent a dark evolution of traditional robbery into the digital age. As cryptocurrency adoption grows across European nations, so does the criminal interest in forcibly extracting these valuable digital holdings from their rightful owners.
This rise in crypto wrench attacks Europe highlights a growing security threat at the intersection of digital finance and physical crime.
Understanding Wrench Attacks
Unlike cybercrime, wrench attacks bypass digital defenses entirely, targeting the human element. Criminals use physical intimidation, kidnapping, or home invasions to force victims into transferring crypto. The irreversible nature of blockchain transactions makes these crimes particularly attractive: once funds are moved, recovery is nearly impossible.
Chainalysis reported that $2.2 billion worth of crypto was stolen globally in 2024, with a growing share linked to coercion and violent crime rather than pure hacking. Europol has warned that organized crime groups are increasingly blending digital intelligence with physical coercion, creating hybrid threats that traditional policing struggle to counter.
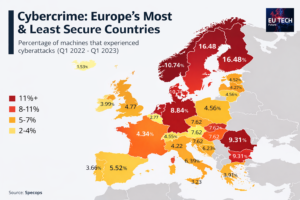
The European Landscape
European law enforcement agencies have documented hundreds of crypto-related violent crimes. In Amsterdam alone, police recorded over 30 cryptocurrency-related violent robberies in 2023, with victims losing millions of euros. Across Germany and the UK, Europol estimates that crypto-related violent incidents rose by nearly 25% between 2022 and 2024.
These attacks range from opportunistic street robberies to elaborate kidnapping schemes. High-profile cases include the abduction of exchange executives and violent home invasions of known investors. Criminals increasingly rely on leaked KYC data and blockchain analytics to identify high-value targets.
Privacy Breaches: The Root of Identity Exposure
The rise in wrench attacks is fueled by privacy breaches:
- Exchange Data Leaks: Breaches expose names, addresses, and trading patterns.
- KYC Exploitation: Centralized storage of sensitive identity data creates honeypots for criminals.
- Social media & Blockchain Analysis: Public posts combined with analytics allow criminals to correlate wallet addresses with real-world identities.
In 2024, an estimated $51 billion flowed to illicit crypto wallets, much of it tracked through stolen identities and coerced transfers.
The EU’s Single Market for Digital Assets: A Regulatory Shield
Europe’s response is a multi-layered framework designed to protect users and strengthen resilience:
- Markets in Crypto-Assets Regulation (MiCAR): Uniform rules for CASPs, focusing on investor protection and transparency.
- Anti-Money Laundering Regulation (AMLR) & Authority (AMLA-R): Centralized oversight of AML/CFT compliance.
- Wire/Funds Transfer Regulation (WTR II): Extends traceability requirements to crypto transfers.
- Digital Operational Resilience Act (DORA): Mandates ICT risk management, resilience testing, and incident reporting.
How WTR II Strengthens Post-Attack Tracking
WTR II extends the “travel rule” to crypto transfers, requiring sender and recipient information to accompany transactions. This makes it harder for criminals to launder stolen assets anonymously through regulated platforms. By ensuring transaction data is available across EU member states, WTR II enhances cross-border monitoring and allows law enforcement to trace stolen funds more effectively. When combined with AMLR and AMLA-R oversight, authorities can flag suspicious transfers linked to wrench attacks and coordinate rapid investigative responses.
Privacy-by-Design: Reducing Exposure
MiCAR requires CASPs to minimize data collection, enforce strict access controls, and purge unnecessary personal information. DORA complements this by mandating regular ICT risk assessments. Together, they reduce the volume of exploitable data available to criminals.
Balancing AML Compliance and Privacy
AML/KYC requirements create honeypots for sensitive data. AMLR and AMLA-R attempt to resolve this by centralizing oversight and mandating stronger safeguards. Privacy-preserving technologies such as zero-knowledge proofs and decentralized identity systems are emerging solutions.
Incident Reporting and Rapid Response
Both MiCAR and DORA emphasize incident reporting. CASPs must notify authorities of breaches, enabling coordinated law enforcement action and early warnings to users.
Industry Compliance and Investment
Compliance requires significant investment: advanced encryption, employee training, and rapid incident response teams. While costly, these measures are essential for legitimacy and user protection.
Outlook: Europe as a Global Model
The EU’s integrated framework positions Europe as a global leader in crypto regulation. With 0.14% of all on-chain transaction volume in 2024 linked to illicit activity, Europe’s proactive stance aims to shrink this share further.
- Global Influence: Europe’s model may become the template for other jurisdictions.
- User Education: Individuals must adopt strong operational security practices – avoiding public disclosure of holdings, using multisig wallets, and maintaining cold storage.
- Adaptive Regulation: Criminal tactics evolve, requiring flexible frameworks that incorporate new technologies and intelligence-sharing mechanisms.
Wrench attacks represent the dark intersection of physical violence and digital finance. They exploit privacy breaches, regulatory gaps, and human vulnerability. Europe’s response, through MiCAR, AMLR, AMLA-R, WTR II, and DORA, is a comprehensive attempt to build a resilient, privacy-conscious crypto ecosystem.
Success will depend on three pillars:
- Regulatory Enforcement
- Technological Innovation
- User Responsibility
If these pillars hold, Europe can significantly reduce the vulnerability of cryptocurrency holders to wrench attacks. More importantly, it can set a global standard for protecting digital assets in an age where the line between cybercrime and physical crime is increasingly blurred.
Also Read: Top 5 Tech Cities in Europe 2026: Where Founders, Funding, and Deep Tech R&D Converge